What is your computer really doing?
We’ve all had a day when our computer seemed a little slower than usual. Most of the time, an update or background process is chewing up the processor’s time. With increasingly complex computers, operating systems, and software, it is difficult to understand exactly what normal is. This complexity can be exploited by malicious actors.
Cyber threats are exploding around us: from ransomware holding data hostage, to state actors conducting espionage, to malware converting devices into botnet nodes. Some of these threats, like rootkits, are hidden out of sight and in places that common tools like antivirus can’t see them. It is increasingly difficult to know if a system is secure.
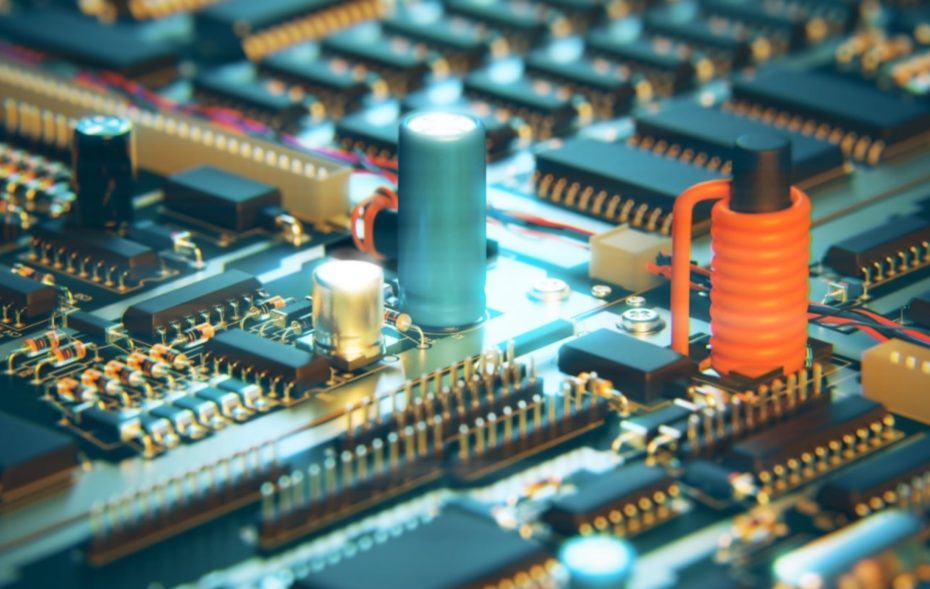
As part of our cybersecurity capability, we’ve developed a technology that can detect and classify a computer’s activity just by listening to it.
“This is exactly the kind of creativity and technical ingenuity that it takes to deliver cybersecurity for the common good in a complex world. “
With a sensitive radiofrequency receiver, our system detects and captures radio energy emissions that are a natural byproduct of every computer logic chip, even from long distances. Then, using information theory and machine learning, we can identify the characteristics of what the computer is processing. For example, sending information out onto a network or writing data out onto a file each have unique signatures. These signatures can be used to find anomalies, sometimes even before the malware is activated, creating an additional layer of safety and security for critical applications.
This is exactly the kind of creativity and technical ingenuity that it takes to deliver cybersecurity for the common good in a complex world. This is what we do at STR.